For decades, Windows has been the default operating system in corporate environments. For many employees, it is the only desktop environment they have ever used. Familiar. Predictable. “Standard.”
But long-standing habits are not always beneficial — especially in cybersecurity.
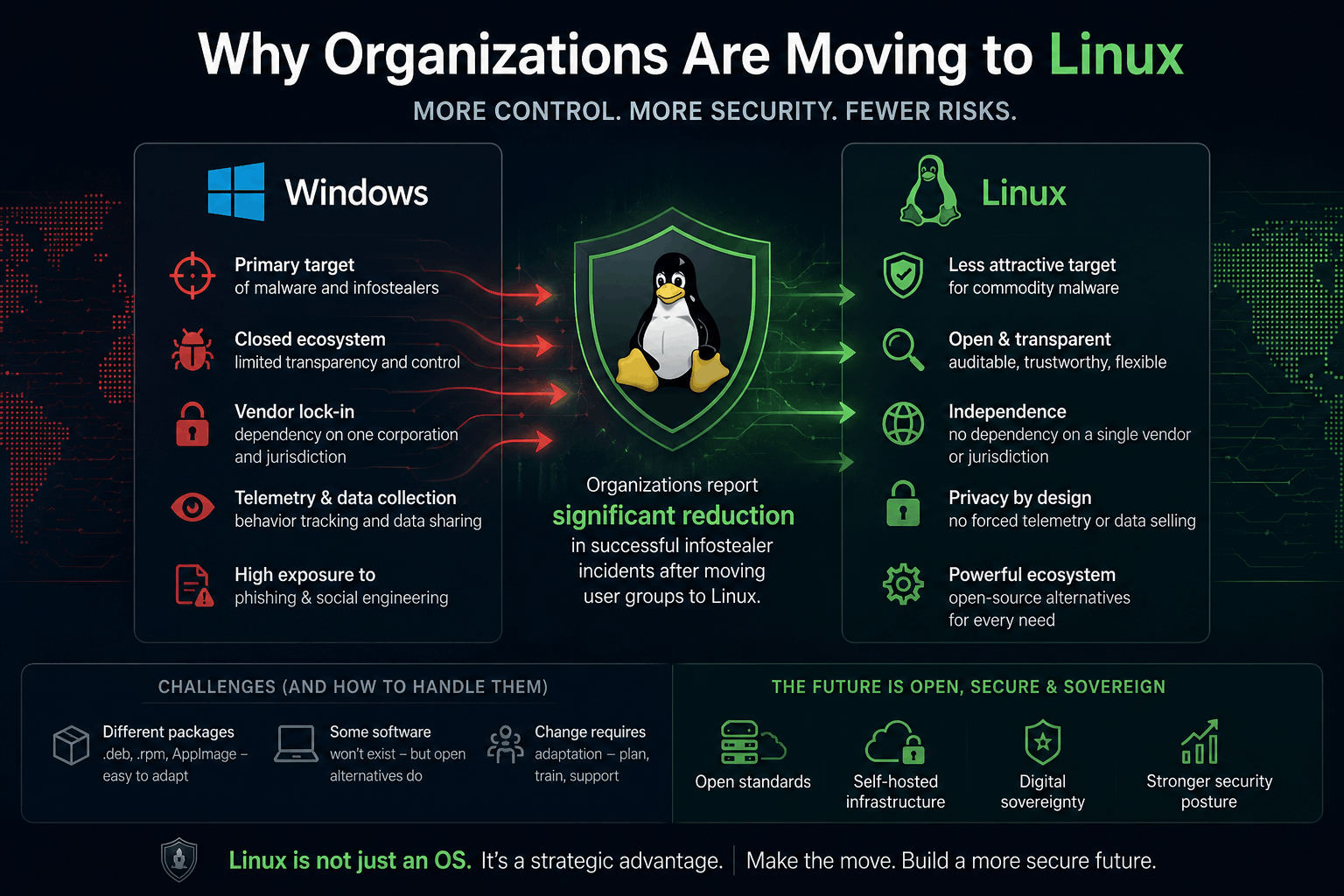
The modern threat landscape is changing faster than most organizations can adapt. Dependency on closed ecosystems, aggressive telemetry collection, vendor lock-in, and increasingly sophisticated malware campaigns force companies to rethink their technological foundations.
And this is where Linux becomes more than just an “alternative OS.”
It becomes a strategic decision.
The Psychological Barrier Is Bigger Than the Technical One
The biggest obstacle in transitioning to Linux is usually not compatibility.
It is fear.
Fear of changing workflows.Fear of learning something new.Fear of losing productivity.
In reality, modern Linux distributions have become dramatically more user-friendly over the last decade. For many office tasks, employees adapt surprisingly quickly — especially when migration is planned correctly and introduced gradually.
The transition is no longer reserved for engineers and system administrators.
Today Linux powers:
- enterprise infrastructure,
- cloud providers,
- financial systems,
- DevOps pipelines,
- embedded systems,
- government platforms,
- and the majority of the internet itself.
The desktop ecosystem is simply catching up.
The Downsides — Honestly
No migration is perfect. Linux also introduces trade-offs organizations should acknowledge upfront.
1. Choosing the Right Distribution Matters
Not all Linux distributions are designed for the same purpose.
Some prioritize:
- enterprise stability,
- long-term support,
- conservative updates,
- and certification compatibility.
Others focus on:
- cutting-edge tooling,
- developer experience,
- flexibility,
- or privacy.
Choosing the wrong distribution for the organization’s workflow can create friction. The migration strategy should align with business needs, not internet trends.
That said, from a security and transparency perspective, many organizations consider Linux ecosystems significantly more trustworthy than proprietary desktop operating systems.
2. Traditional .exe Workflows Disappear
Windows users are accustomed to downloading and launching .exe installers.
Linux works differently.
Depending on the distribution, software is commonly distributed as:
- .deb
- .rpm
- universal packages like AppImage
- Flatpak
- Snap
This requires some adaptation, but it also introduces stronger package management practices and centralized software verification mechanisms.
Ironically, this learning curve often reduces unsafe “download random executable from the internet” behavior.
3. Some Familiar Software Will Not Exist
Certain proprietary applications simply do not support Linux.
However, in many cases:
- open-source alternatives already exist,
- web-based replacements are sufficient,
- or organizations discover they were overpaying for software features they rarely used.
Examples include:
- LibreOffice replacing Microsoft Office,
- GIMP or Krita for graphics workflows,
- Thunderbird for email,
- Jitsi or Matrix-based communication platforms,
- Blender replacing expensive proprietary 3D tooling in many pipelines.
Blender is a particularly interesting example.
For years it was dismissed as a “non-professional” alternative. Today it is used by studios, researchers, independent creators, and enterprise teams worldwide.
The pattern repeats itself across software categories.
The Advantages Organizations Cannot Ignore
1. Open Ecosystems Reduce Certain Supply Chain Risks
Closed software vendors aggregate enormous amounts of telemetry and user data.
Even when vendors themselves are trustworthy, centralized ecosystems become highly attractive targets for attackers.
Open-source ecosystems do not magically eliminate risk — but they change the trust model:
- source code can be audited,
- telemetry can be controlled,
- software behavior is more transparent,
- and organizations gain more operational independence.
This matters increasingly in sectors dealing with:
- sensitive data,
- regulated industries,
- defense,
- healthcare,
- finance,
- and critical infrastructure.
2. Linux Is Still a Less Attractive Target for Commodity Malware
The majority of mass-market malware ecosystems are still heavily focused on Windows environments.
This includes:
- infostealers,
- fake installers,
- malicious Office macros,
- clipboard hijackers,
- loader malware,
- and scam-driven social engineering kits.
Attackers target scale.
And today, the largest ecosystem for opportunistic attacks remains Windows desktops.
Linux is not “immune.”
That is a dangerous myth.
But many attack chains become:
- more difficult to execute,
- less automated,
- less profitable,
- or require significantly more expertise from attackers.
This alone changes the economics of cybercrime.
3. Reduced Dependency on a Single Vendor and Jurisdiction
Technology is no longer purely technical.
It is geopolitical.
Organizations increasingly recognize the risks of depending entirely on:
- one corporation,
- one cloud ecosystem,
- one licensing model,
- or one political jurisdiction.
This is one of the reasons why parts of Europe have already begun transitioning away from certain “US Big Tech” dependencies toward:
- sovereign infrastructure,
- self-hosted services,
- open standards,
- and open-source software.
Examples include migrations from:
- Windows to Linux,
- Microsoft Office to LibreOffice,
- proprietary document formats to open standards like .odt.
The motivation is not ideology alone.
It is operational resilience.
4. Significant Reduction in malware Incidents
One of the most overlooked advantages of Linux desktop deployments is the measurable reduction of commodity credential theft attacks in some industries.
Organizations whose employees are frequently exposed to:
- phishing,
- malicious attachments,
- fake browser updates,
- pirated software,
- and social engineering campaigns
have reported substantial decreases in successful infostealer infections after migrating critical user groups away from Windows-centric workflows.
Why?
Because many large-scale infostealer and other malware operations are optimized specifically for:
- Windows credential stores,
- browser data extraction,
- Microsoft authentication tokens,
- and common Windows enterprise desktop configurations.
Changing the operating environment disrupts attacker automation.
Again, Linux is not invulnerable.
Targeted attacks remain possible.
But removing the “default target” advantage from cybercriminals can dramatically improve an organization’s defensive position.
Linux Is Not About Ideology
This is important.
Linux should not be treated as a religion, political statement, or internet subculture.
It is simply another operating system.
But unlike many traditional enterprise ecosystems, it offers:
- transparency,
- flexibility,
- auditability,
- independence,
- and control.
For organizations seriously thinking about long-term cybersecurity resilience, those qualities are becoming increasingly difficult to ignore.
The question is no longer:
“Can organizations work on Linux?”
The real question is:
“How long can organizations afford to remain entirely dependent on ecosystems that were never designed with transparency or operational sovereignty in mind?”